
Why Behavior Allow-Listing Beats Endless Detection Rules in Container Security (Part 2)
Modern container environments move fast, and so do attackers. Traditional security approaches based on signature matching or static detection rules are...
32 posts in this category

Modern container environments move fast, and so do attackers. Traditional security approaches based on signature matching or static detection rules are...

Modern container environments move fast, and so do attackers. Traditional security approaches based on signature matching or static detection rules are...
As NIS2 has become law in Sweden, we continue to explore the impact it will have on software engineering teams....
The shift from virtual machines to containers and Kubernetes fundamentally changed how software is built, shipped, and operated. Infrastructure became...
Hallucinated dependencies become a vulnerability when attackers exploit common package names generated by AI models. This is called slopsquatting, and it is a...

Alerts are pouring in. Your team’s stretched. And the critical signal is buried in noise.Bifrost flips the model: we understand each service’s legit runtime...

Here’s how your company can cut costs without compromising on security by using bifrost:⚙️Automate manual processes⚠️Prevent costly breaches️Protect the...
Europe relies heavily on foreign tech giants, the issue of digital sovereignty has become more crucial than ever. It’s not just about where your servers are...
As a driving force behind innovation across nearly every industry, AI tools have revolutionised the software development landscape. In cybersecurity, AI brings...
We know there’s plenty of security tools out there. But bifrost is built to do more than just alert you. It protects you automatically, from testing to...

Are you sure that your security controls are adequate in practice, not just on paper? Every day, companies spend money on tools, policies, and processes that...
AI-generated code is quickly becoming a central part of modern software development. These AI agents can write, test, and deploy code with minimal human input,...
Stop firefighting security threats and focus on what matters, building and shipping innovative products. bifrost automates security, empowering developers,...
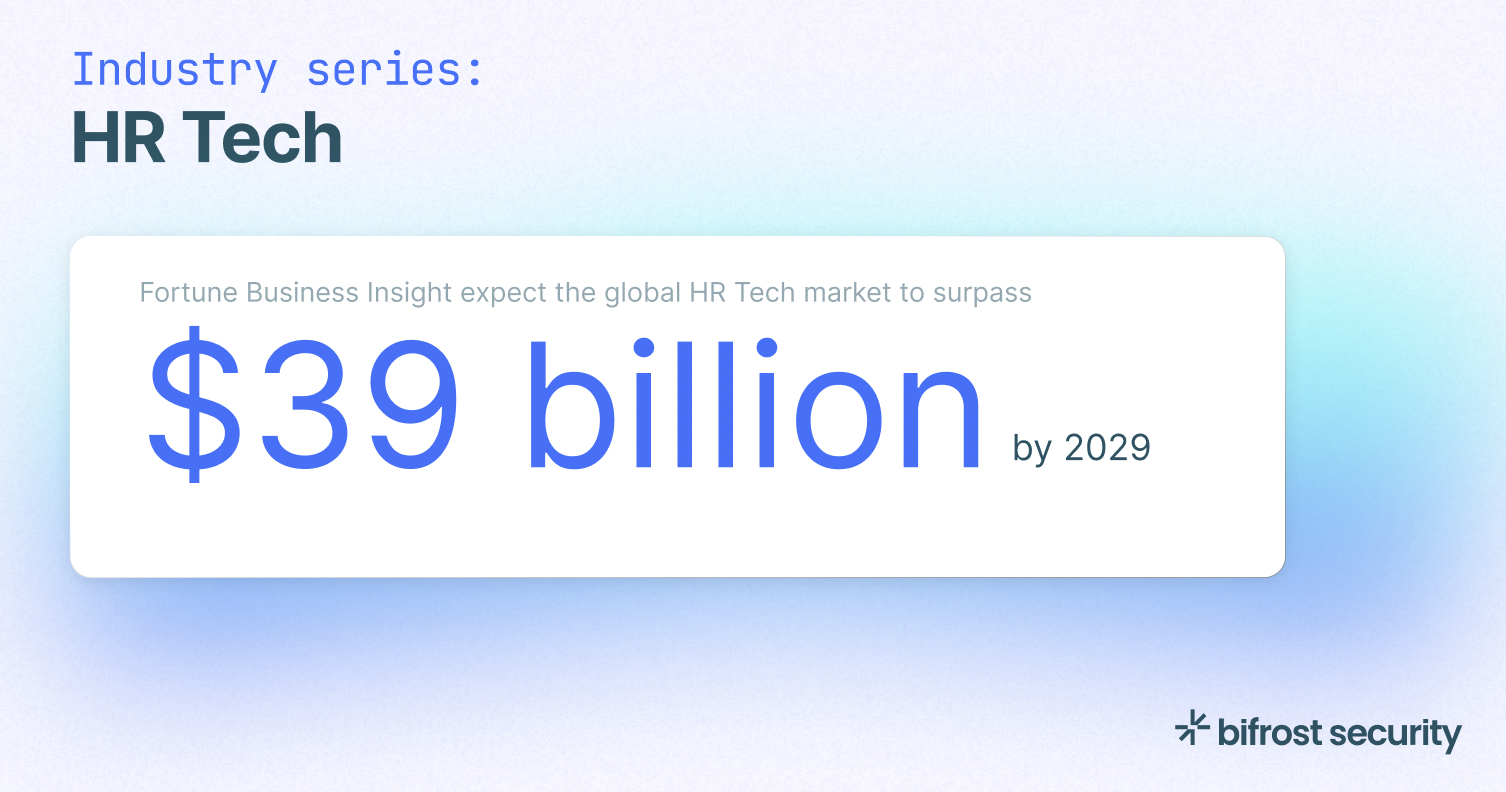
The evolution of HR Technology is transforming how organizations attract, retain, and engage talent. As workforce expectations shift and hybrid models become...
You’ve written the policies. You’ve stored the logs. But are you confident that your security controls are working in practice, or just on paper?...

Did you know the UK online gambling market generated over £15 billion in 2023? As the industry grows, so do the security challenges it faces. In the fast-paced...

In a week bifrost security is co-hosting an evening with **QA.tech** and ** Netlight** to explore how DevOps and DevSecOps teams are using AI to deliver...
**For DevOps ⚙️** We get it, DevOps is all about speed, reliability, and efficiency. But security? It often feels like an afterthought. Traditional security...
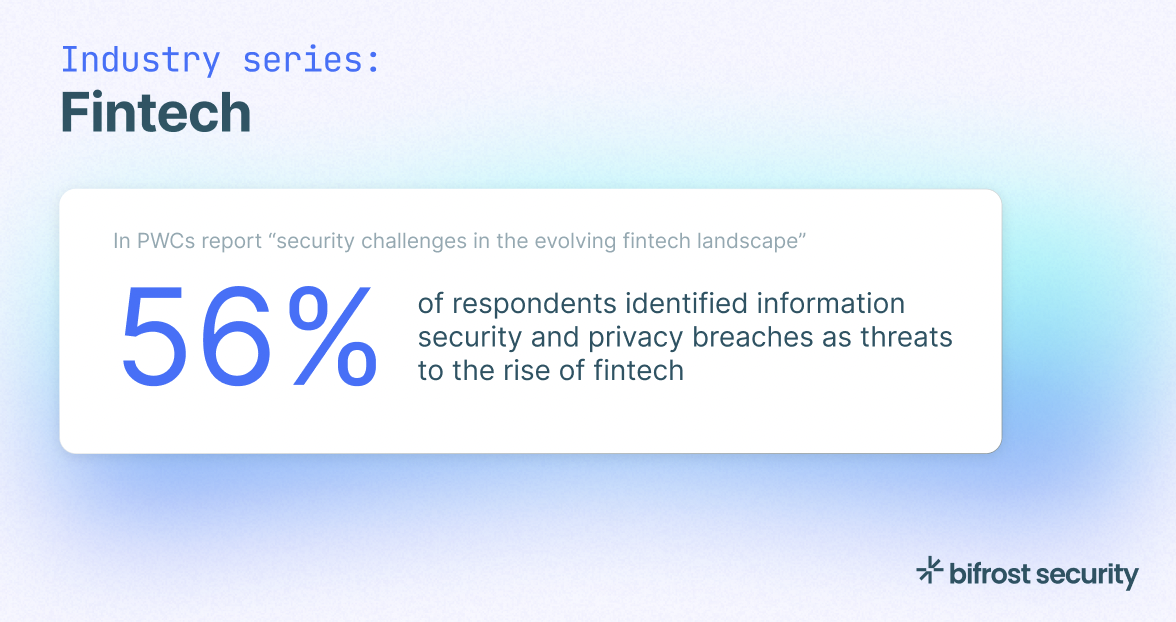
From mobile transfers and electronic payments to cryptocurrency trading, the fintech industry is improving the efficiency and convenience of the financial...
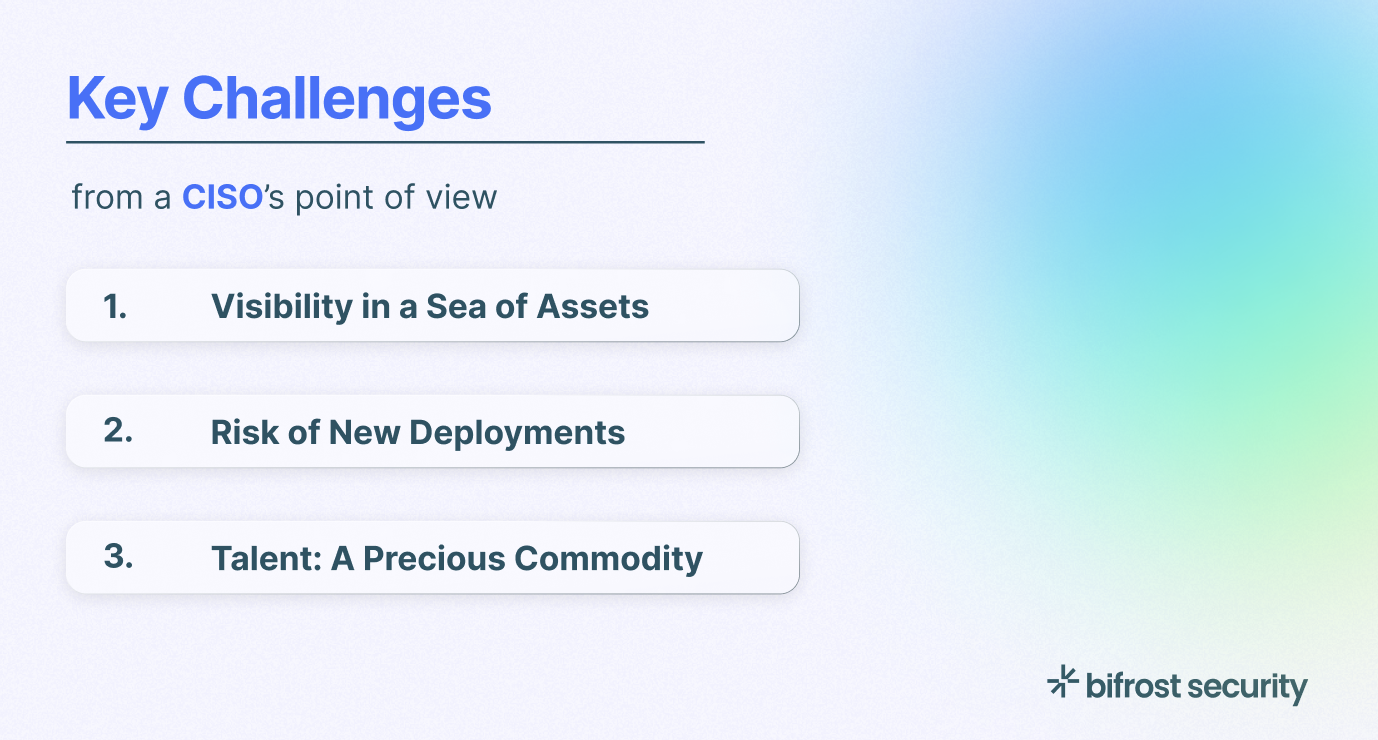
With rising cybersecurity threats, increasing legal scrutiny and the introduction of security regulations, CISOs are under significant pressure. In the annual...
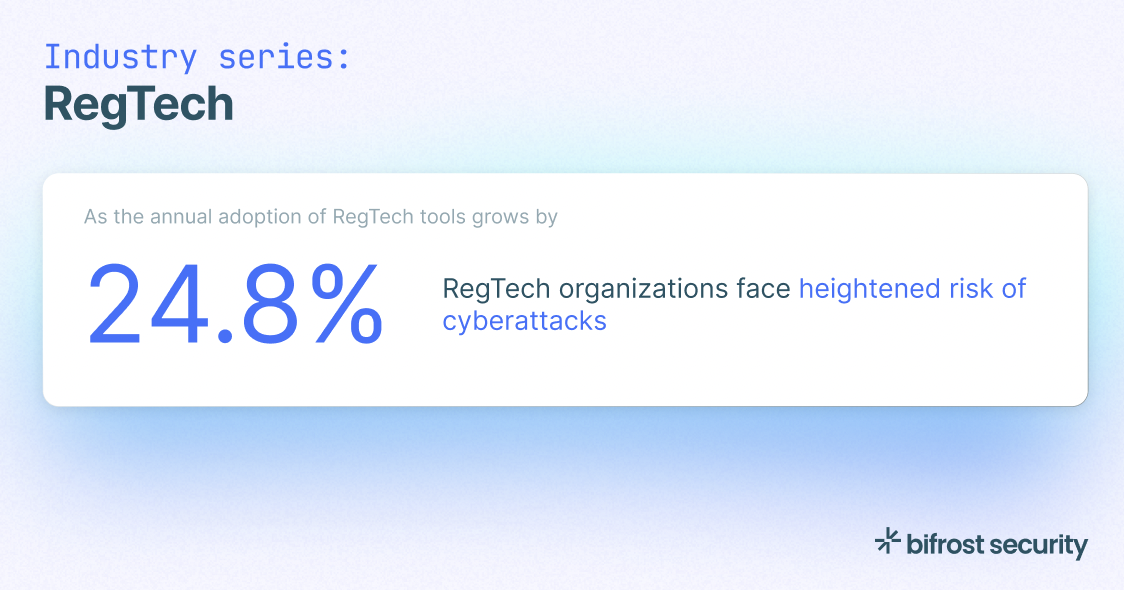
The rise of RegTech is reshaping how businesses manage compliance and risk. As regulatory demands grow, more companies turn to RegTech providers to streamline...

Over the last decade, software, cloud computing and AI have increasingly been incorporated into healthcare. This has caused healthcare to move to online...

As 2024 has come to an end, we take a look back at last year's Kubernetes environment. In a recent study by Redhat, insights from 600 professionals across...

In the report “Protecting the Cloud Native Enterprise: Build the Foundation to Secure Your Containers in Runtime” by @Aqua, 90% of global organizations are...

Over the last decade, software, cloud computing and AI have increasingly been incorporated into healthcare. This has caused healthcare to move to online...
In the wake of the ongoing global transformation, cybersecurity's challenges have taken on new dimensions. The COVID-19 pandemic has accelerated changes,...
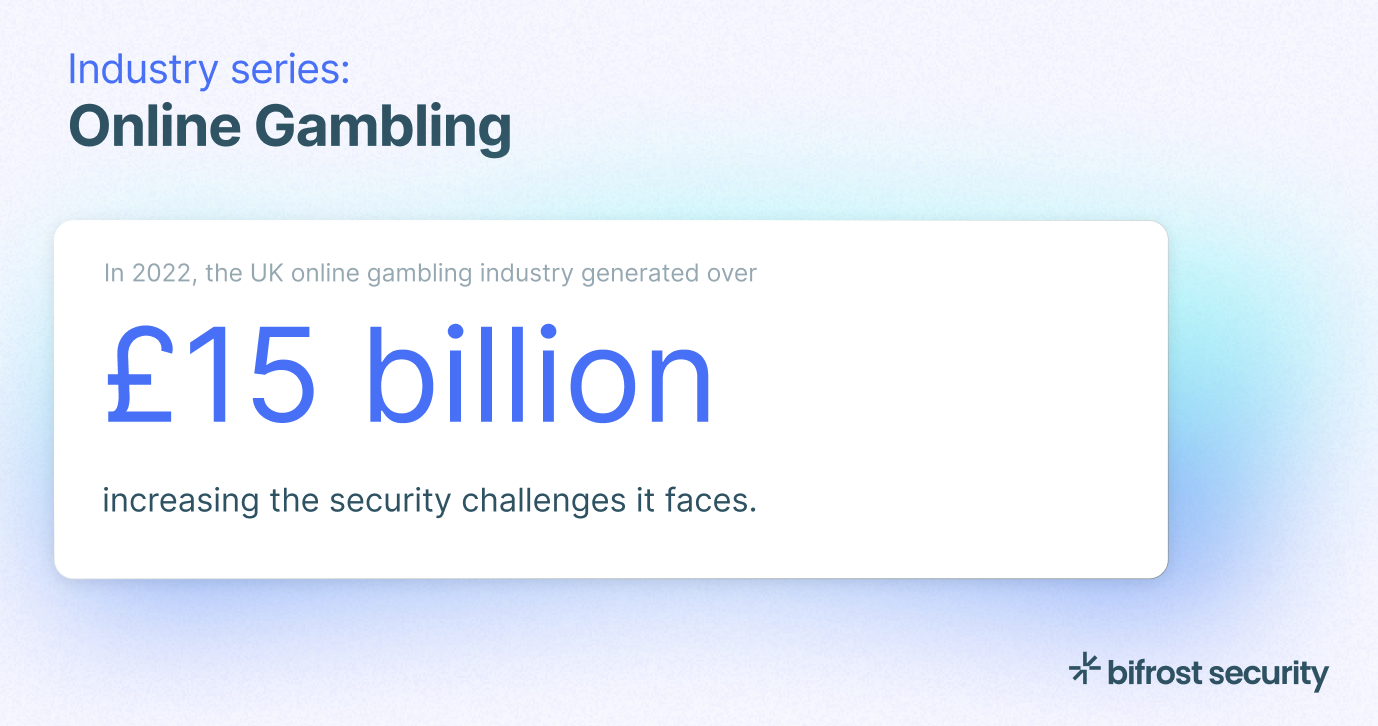
Did you know the UK online gambling market generated over £15 billion last year? As the industry grows, so do the security challenges it faces. In the...
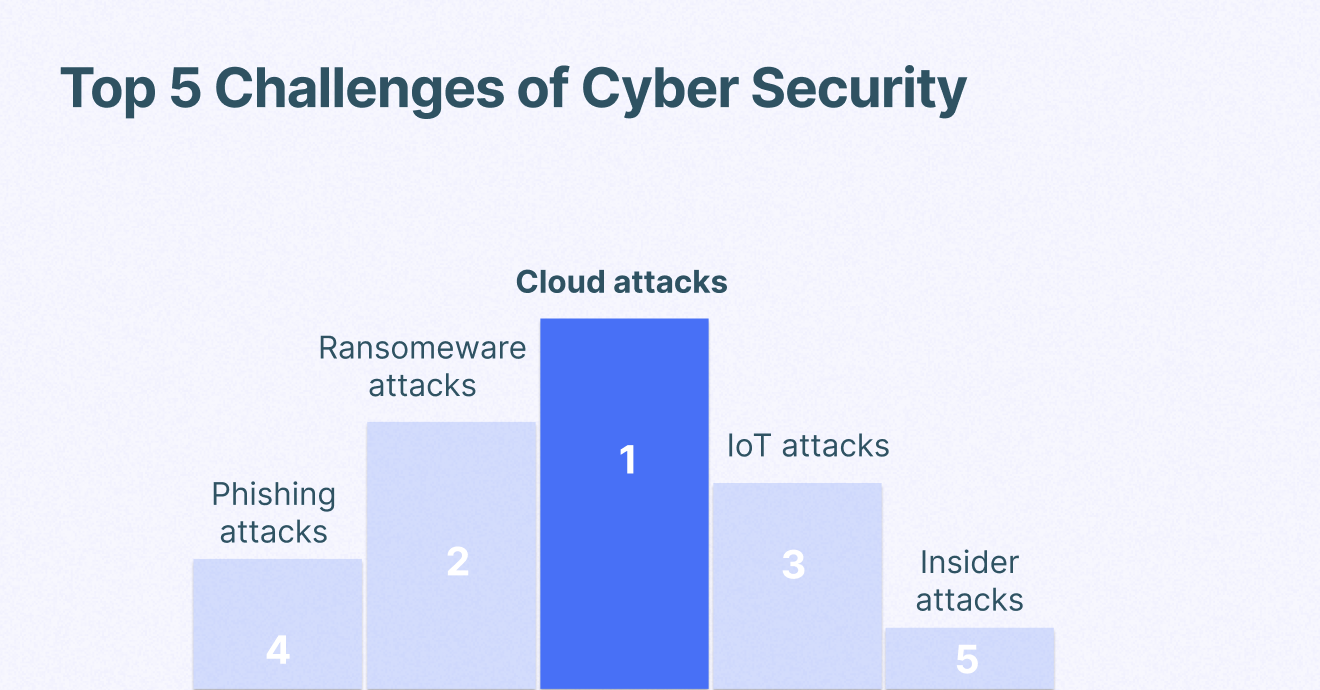
Cyber security breaches have been projected to cost 8 trillion USD a year in damages. Comparable to the world's third-largest economy, following the US and...

bifrost attended the ONE Conference in the Hague last week. We participated in great discussions and presentations. Here are our key takeaways from the event...
In 2024, the need to secure your software supply chains has become more evident than ever. A recent Software Supply Chain Security (SSCS) report by Checkmarx...
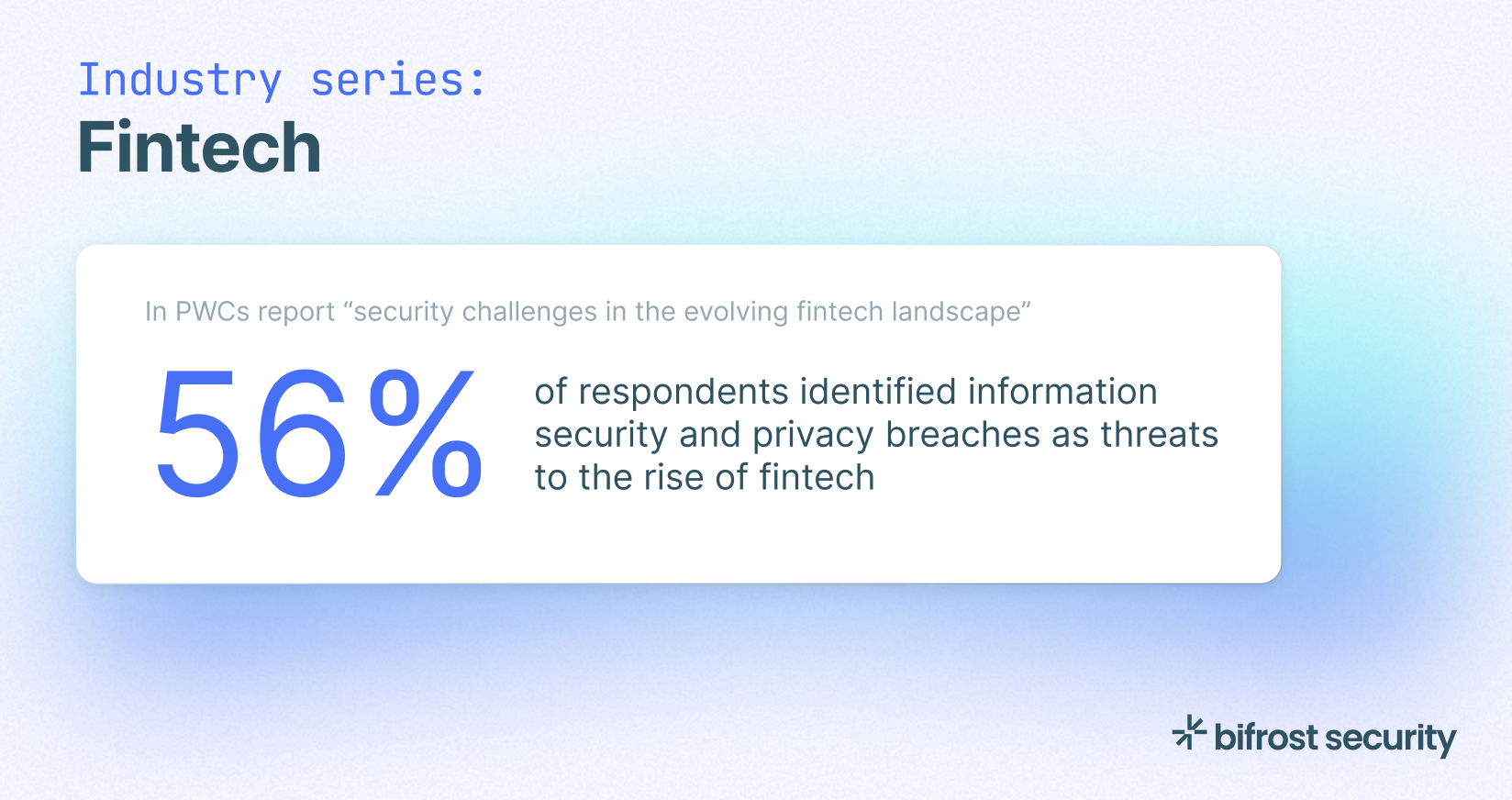
From mobile transfers and electronic payments to cryptocurrency trading, the fintech industry is improving the efficiency and convenience of the financial...
The growing landscape of cloud computing has revolutionized the way modern applications are built. Bringing a wave of agility, automation, and innovation....